Security researchers say a powerful new Android malware masquerading as a critical system update can take complete control of a victim’s device and steal their data.
The malware was found bundled in an app that had to be installed outside of Google Play, the app store for Android devices. Once installed by the user, the app hides and stealthily exfiltrates data from the victim’s device to the operator’s servers.
Researchers at mobile security firm Zimperium, which discovered the malicious app, said once the victim installs the malicious app, the malware communicates with the operator’s Firebase server, used to remotely control the device.
The spyware can steal messages, contacts, device details, browser bookmarks and search history, record calls and ambient sound from the microphone, and take photos using the phone’s cameras. The malware also tracks the victim’s location, searches for document files, and grabs copied data from the device’s clipboard.
The malware hides from the victim and tries to evade capture by reducing how much network data it consumes by uploading thumbnails to the attacker’s servers rather than the full image. The malware also captures the most up-to-date data, including location and photos.
Zimperium CEO Shridhar Mittal said the malware was likely part of a targeted attack.
“It’s easily the most sophisticated we’ve seen,” said Mittal. “I think a lot of time and effort was spent on creating this app. We believe that there are other apps out there like this, and we are trying our very best to find them as soon as possible.”
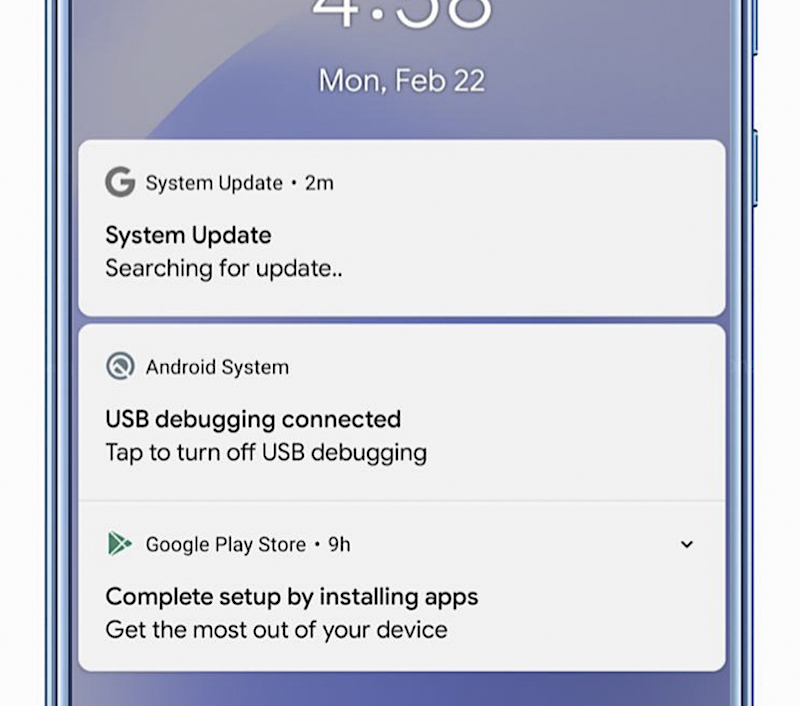
A screenshot of the malware masquerading as a system update running on an Android phone. The malware can take full control of an affected device. (Image: Zimperium)
Tricking someone into installing a malicious app is a simple but effective way to compromise a victim’s device. It’s why Android devices warn users not to install apps from outside of the app store. But many older devices don’t run the latest apps, forcing users to rely on older versions of their apps from bootleg app stores.
Mittal confirmed that the malicious app was never installed on Google Play. When reached, a Google spokesperson would not comment on what steps the company was taking to prevent the malware from entering the Android app store. Google has seen malicious apps slip through its filters before.
This kind of malware has far-reaching access to a victim’s device comes in a variety of forms and names, but largely does the same thing. In the early days of the internet, remote access trojans, or RATs, let snoops spy on victims through their webcams. Nowadays, child monitoring apps are often repurposed to spy on a person’s spouse, known as stalkerware or spouseware.
Last year, TechCrunch reported on the KidsGuard stalkerware — ostensibly a child monitoring app — that used a similar “system update” to infect victims’ devices.
But the researchers don’t know who made the malware or who it’s targeting.
“We are starting to see an increasing number of RATs on mobile devices. And the level of sophistication seems to be going up, it seems like the bad actors have realized that mobile devices have just as much information on them and are much less protected than the traditional endpoints,” said Mittal.
Send tips securely over Signal and WhatsApp to +1 646-755-8849. You can also send files or documents using SecureDrop.